[ad_1]
A secret U.S. Navy program that aims to improve information sharing among military forces is taking shape.
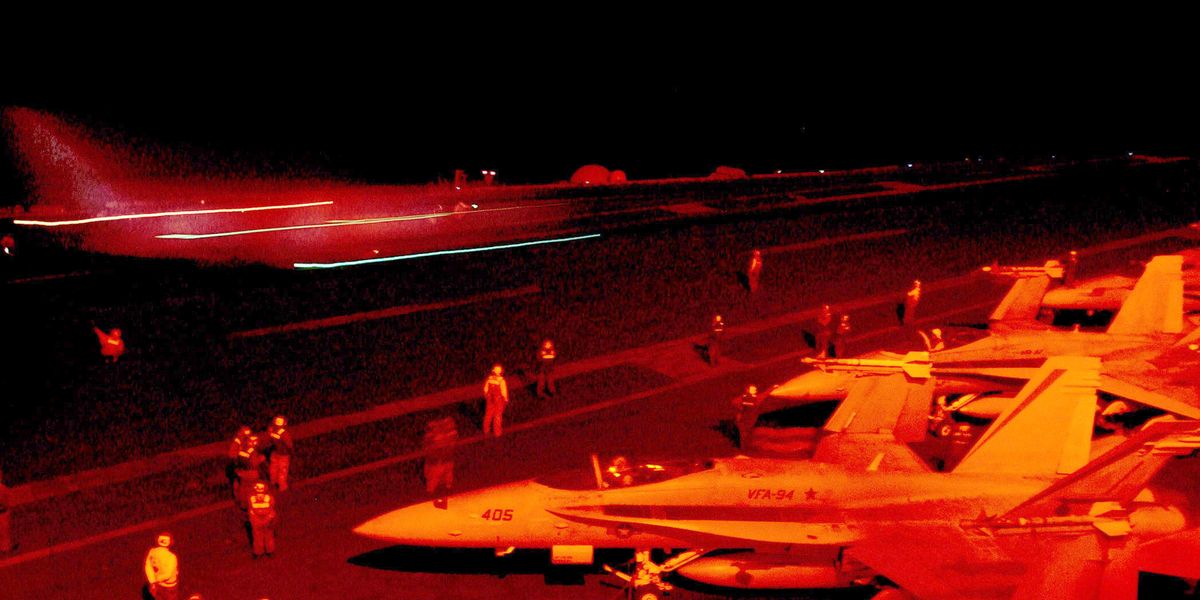
Project Overmatch is being tested with the Carl Vinson Carrier Strike Group off the California coast. The project is part of the Pentagon’s multi-billion-dollar Joint All-Domain Command and Control (JADC2) effort, which is intended to establish seamless communication and give warships better awareness of adversaries at sea.
“Fundamentally, this is all about management of data, exchange of data,” David Deptula, the dean of the Mitchell Institute for Aerospace Studies and a retired Air Force lieutenant general, said at an industry event, via Defense News. “Without the appropriate infrastructure, you can’t be able to do the data, connectivity or networking. Without the security, all of it falls apart because you’re yielding a huge weakness and vulnerability to our adversary.”
More From Popular Mechanics

Better Connections
The details of Project Overmatch are closely guarded secrets, but it’s reportedly centered around a system that would allow the Navy to push software updates among units and share critical information in real time. The Navy eventually plans to install the required hardware and software on all 11 carrier strike groups, Defense News reports.
The Navy is seeking $192 million for Project Overmatch for Fiscal Year 2024, less than the $226 million allotted to the effort this year.
Project Overmatch isn’t working in a vacuum. The program is the Navy’s contribution to JADC2, a concept that the Department of Defense has developed to connect sensors from all branches of the armed forces into a unified network. JADC2 uses artificial intelligence and machine learning to help the military quickly sense and act on information across the battlespace.
Potential adversaries are gearing up for their own versions of JADC2. China is developing its concept of Multi-Domain Precision Warfare—a combination of computers, intelligence, surveillance, and reconnaissance to coordinate firepower and expose enemy weaknesses—according to the U.S. military’s annual China Military Power Report.
An article from the Department of Defense states that the concept is “intended to help identify key vulnerabilities in an adversary’s operational system, and then to launch precision strikes against those vulnerabilities. These could be kinetic or non-kinetic.”
“Basically,” a senior defense official said in the China Military Power Report, “it’s a way that they’re thinking about looking across domains to identify vulnerabilities in an adversary’s operational system and then to exploit those to cause its collapse.”

Science and Technology Journalist
Sascha Brodsky, a freelance journalist based in New York City and a graduate of the Columbia University Graduate School of Journalism and Columbia’s School of International and Public Affairs, writes about many aspects of technology including personal technology, AI, and virtual reality. His work has appeared in The New York Times, The Atlantic, The Guardian, and many other publications. In his spare time, he enjoys cycling and hiking.
[ad_2]
Source link